Togel Membuatmu Ketagihan adalah singkatan dari "Toto Gelap", sebuah jenis permainan judi yang sangat populer di beberapa negara, terutama di...
Understand About A lottery is a type of gambling where participants purchase tickets for a chance to win a prize,...
Legendary Treasures Slot Online Unraveling the Mysteries of the Past have long captured the imaginations of people around the world....
Maeltoto Bandar Togel Online Terpercaya Pasaran TerlengkapKKRC300Sebagai bandar togel terpercaya dengan pasaran terlengkap, Maeltoto menawarkan pengalaman bermain togel yang unggul...
Pandangan Positif & Negative Judi online adalah bentuk perjudian yang dilakukan melalui internet menggunakan perangkat seperti komputer, ponsel cerdas, atau...
Mengatasi Cara Bermain Judi online adalah bentuk perjudian yang dilakukan melalui internet menggunakan perangkat seperti komputer, ponsel cerdas, atau tablet....
Pragmatic Play Permainan dan Kentungan adalah salah satu penyedia perangkat lunak perjudian terkemuka di industri perjudian online. Mereka dikenal karena...
Mengetahui Bagaimana Cara Scatter adalah simbol khusus yang dapat muncul di gulungan tanpa harus berurutan atau dalam garis pembayaran yang...
Jam Terbaik Bermain Slot Online Maeltoto 2024 KKRC300 Saat mempertimbangkan "jam terbaik" untuk bermain slot online di Maeltoto atau platform...
Golden Dragon Slots Online - In the vast and dynamic world of online casino gaming, Golden Dragon slots stand out...
Slot Gates of Olympus adalah slot online yang membawa pemain ke dalam dunia mitologi Yunani kuno yang penuh dengan dewa...
Seperti kebanyakan permainan slot, menang dalam "Gates of Olympus" didasarkan pada keberuntungan dan tidak ada strategi pasti yang dapat menjamin...
Jumat Kliwon Slot Online adalah slot online yang mengangkat tema mistis dan keberuntungan, menawarkan pengalaman bermain yang penuh dengan misteri...
Mengeksplorasi Dragon Tiger Wild, sebuah konsep yang menggabungkan dua makhluk mitologis yang legendaris, menjanjikan petualangan yang mengasyikkan dan keajaiban alam...
Menyelami Provider PG SOFT, sebagai salah satu penyedia permainan judi online yang inovatif dan saat ini berada di puncak industri...
Menyelami Keunikan Pragmatic Play - telah mengukuhkan dirinya sebagai salah satu penyedia permainan slot online terkemuka di industri perjudian. Dengan...
Mengintip Masa Depan Slot Gambling - Dalam dunia perjudian daring yang terus berkembang, industri slot gambling telah menjadi salah satu...
How to Win Realistically at Toto Slots Without Cheating - The majority of gamblers playing Toto slots on online roda4d...
How the Online Gambling Business Works You Need to Know - Online gambling is a huge industry, with millions of...
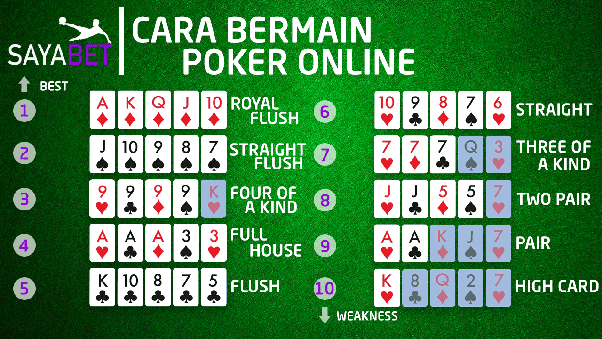
Tips Orang Dalam untuk Menjadi Pemain Poker yang Sukses - Jika Anda adalah seseorang yang sangat suka bermain poker online...
Intermediate Bingo Strategies You Can Apply - Bingo is a game of chance that is meant to be played for fun....
Strategi Bingo Tingkat Menengah yang Bisa Anda Terapkan - Bingo adalah permainan untung-untungan yang dimaksudkan untuk dimainkan demi kesenangan. Namun itu...
Different Types of Poker You Should Try At Least Once - No matter where in the world you are, you have probably...
Berbagai Jenis Poker yang Harus Anda Coba Setidaknya Sekali - Tidak peduli di belahan dunia mana Anda berada, Anda mungkin pernah mendengar, melihat,...
How to Play Under the Gun at Poker is a game that involves taking risks with limited knowledge, but what happens if...
Cara Bermain Under the Gun di Poker adalah permainan yang melibatkan pengambilan resiko dengan pengetahuan yang terbatas, namun apa jadinya jika pengetahuan...
How to Choose Winning Numbers in Playing Keno - Keno was introduced by an ancient Chinese ruler named Cheung Leung as...
Cara Memilih Nomor Pemenang dalam Memainkan Keno - Keno diperkenalkan oleh penguasa Tiongkok kuno bernama Cheung Leung sebagai sarana untuk mendanai biaya...
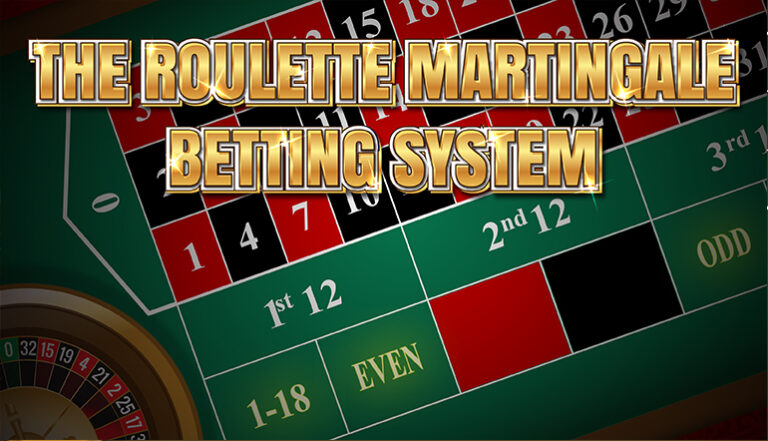
Explanation of the Martingale System When Gambling - The Martingale System is a betting strategy that tells you how much to bet...
Penjelasan Tentang Sistem Martingale Saat Bermain Judi - Sistem Martingale adalah strategi taruhan yang memberi tahu Anda berapa banyak yang harus dipertaruhkan pada...